Ransomware is the most prominent and disruptive type of malware currently in existence. A single attack can cause millions of dollars in damages and require hundreds of hours of recovery before the victim can start using the infected devices again.
This article is an introduction to ransomware and the dangers of extortion software. We explain what this malware is and how it works, examine the current ransomware landscape, and offer advice on how best to counter this cyber threat.

Ransomware Definition
Ransomware is an ever-evolving malware that blocks access to files or devices until the victim pays a ransom. Most ransomware use encryption to make data unusable, allowing attackers to demand money in exchange for the decryption key. If the victim ignores the demand, the attacker deletes the key and, as a result, makes all encrypted data useless.
Ransomware can infect a single PC or a mobile device, but an attack can also go after an entire network. The motive is usually monetary, but some attacks primarily aim to sabotage the target. The consequences of ransomware can be crushing and lead to:
- Loss of business and customer data.
- Legal repercussions for allowing a data breach.
- Prolonged downtime.
- A reputation hit that leads to a loss of customers.
- A costly recovery process that takes weeks to restore the network to a pre-attack state.
- Long-term damage to infrastructure.
Ransom requests range from a few hundred dollars to millions. Most attackers demand payment in Bitcoins, a choice of currency that allows the criminal to remain anonymous after receiving the money.
Hackers use ransomware to target SMBs, enterprises, public organizations, and individual users. This type of malware is also a danger to all OSs, including Windows, Linux, and Mac. No business or system is safe, so ransomware prevention must be a part of every cybersecurity strategy.
Read about cybersecurity best practices that help counter ransomware and other prominent online threats.
The Current State of Ransomware
Ransomware continues to evolve as criminals work on new tactics for exploiting the advances in cloud computing, virtualization, and edge computing. Below are the most notable trends currently shaping the ransomware landscape:
- Pressure on MSPs: Criminals are targeting managed service providers (MSPs) more than ever before. Breaching a single MSP creates an opportunity to infect clients and allows an attacker to go after multiple targets with a single breach.
- Better defenses: Companies are trying to stay ahead of hackers with new tactics. Improved heuristics, behavior analysis, and bait files are helping companies predict attacks instead of responding to dangers.
- Targeting work-from-home companies: Hackers are continuing to go after teams that operate remotely. Employees using personal devices to work from home are the prime target.
- Focus on industries in disarray: Attackers continue to prey on sectors that took a hit from the pandemic. Healthcare and education facilities are most vulnerable as criminals know their data is valuable and likely poorly protected.
- More RaaS than ever: Ransomware-as-a-Service is a subscription-based “service” that allows hackers to use third-party tools to carry out attacks. Tool creators get a percentage of each successful breach, while “clients” get to focus entirely on spreading malware.
- Biggest threats: The most prominent ransomware in 2021 are Conti, Avvadon, REvil (ex Sodinokibi), Netwalker, and Babuk. The most common attack vectors remain phishing emails, RDP exploits, and software weaknesses.
Our article about ransomware statistics presents eye-opening facts that demonstrate the danger behind this cyber threat.

How Does Ransomware Work?
All ransomware attacks start with an initial infection when a malicious payload enters the system. Once the program is within the system, the ransomware executes a malicious binary. Depending on the type of malware, the goal of the payload is to:
- Automatically search for target data (Microsoft Word documents, images, databases, etc.) and starts encryption.
- Connect to the hacker’s C&C server and grant direct control over the system.
- Automatically lock the operating system and device.
- Search for valuable data and set up the exfiltration process.
Once the program completes its task, the user loses access to files or the entire computer. The device displays a message explaining that the system is the victim of ransomware and that the only way to regain control or retrieve data is to pay a ransom. The two common ways programs display this message are:
- A background that changes to a ransom note.
- Text files within each encrypted directory.
Typically, every ransom has two deadlines to put pressure on the victim. The first deadline is when the hacker threatens to double the ransom, while the other is when the attacker plans to delete the decryption key.
Most ransomware relies on asymmetric encryption. This type of cryptography uses a pair of unique keys to encrypt and decrypt data. One key encrypts the victim’s files, and the only way to retrieve data is to use the key stored on the hacker’s server. Most ransomware programs use a different decryption key for each target file.
A cyber kill chain allows a security team to define each step in a ransomware attack and use it as an opportunity to detect and stop the threat.
How Does Ransomware Spread?
Here are the most common methods criminals use to spread ransomware:
- Email phishing campaigns that spread a corrupt link or attachment.
- A highly targeted spear-phishing attack.
- Different forms of social engineering (baiting, scareware, pretexting, tricks on social media, etc.).
- Malvertising.
- Exploit kits on malicious websites.
- A custom worm that exploits a system weakness (such as a faulty RDP setup or a flaw due to poor server management).
- An infected piece of hardware (namely USBs and laptops).
- Unwanted add-ons during downloads.
Most top-tier ransomware can spread via the network after infecting the initial victim. In many cases, the infected device is an endpoint and not the objective of the attack. Typical targets are databases and servers, so most programs use self-propagating mechanisms to spread to other systems.

Who Does Ransomware Target?
Ransomware criminals attack anyone they can, but their primary targets are companies that seem willing to pay a hefty ransom quickly. Most attacks go after victims that:
- Keep valuable client data (for example, banks or law firms).
- Require immediate access to files (hospitals and clinics).
- Have irreplaceable data (government agencies).
- Rely on an understaffed security team (public institutions and SMBs).
- Have a disparate user base and a lot of file sharing (universities).
Do not feel safe if your business does not fall under these criteria. Criminals are opportunistic and will not miss a chance to go after anyone vulnerable. Also, some ransomware spreads automatically across the Internet, so every company is a potential target regardless of size, industry, or income level.
Learn how ransomware is delivered.
How Many Types of Ransomware Are There?
While all ransomware programs follow a similar blueprint, there are two main types of these cyberattacks:
- Locker ransomware (computer locker): A type of malware that locks users out of their device and prevents the computer from booting up. Typically, the locked system allows limited access so that the victim can interact with the hacker.
- Crypto ransomware (data locker): An attack that encrypts valuable data without locking the user out of the device. Usual targets are financial data, private customer info, large work projects, photos, tax info, videos, etc.
Locker ransomware is the less dangerous type as these attacks do not move over the network or corrupt files. This malware is also easier to remove without paying the ransom, which is why locker hackers often act as police officers to pressure the victim into paying quickly.
When companies began to rely on better data backups, criminals started to work on a new ransomware variant. A Doxware attack looks to exfiltrate data from the target system. If the program steels the data, the attacker demands a ransom with the threat of leaking files or selling them to the highest bidder.
Some programs can first exfiltrate the data and then encrypt files. A mix of crypto and Doxware capabilities allows an attacker to use both extortion tactics.
Our article about different ransomware examples provides an in-depth look at the world’s most notorious extortion programs.
How to Avoid Ransomware?
Ransomware can be hard to stop, but a combination of employee awareness, proactive response planning, and basic security hygiene can help. Below are the best practices every business should implement to protect against ransomware:
- Keep devices and systems up to date with the latest security patches.
- Ensure the team uses strong email security practices.
- Organize security awareness training to ensure the team knows how ransomware works.
- Use network segmentation to prevent lateral movement between systems.
- Ensure employees know how to use anti-malware and virus solutions.
- Emphasize the importance of safe surfing to avoid malicious ads and drive-by downloads.
- Improve overall network security.
- Rely on zero-trust policies and multi-factor authentication to protect vital systems and databases.
- Monitor network activity for suspicious behavior.
- Ensure endpoints do not become an entry point with regular updates and traffic monitoring.
- Create an incident response plan.
The best way to minimize the threat of ransomware is to use immutable backups. This type of backup is uneditable, so intruders cannot encrypt, delete, or alter the info. Back up data multiple times per day to minimize the risk of losing data if ransomware strikes.
Our article about ransomware prevention presents 18 security practices and measures that help keep this cyber threat at bay.
What to Do in Case of a Ransomware?
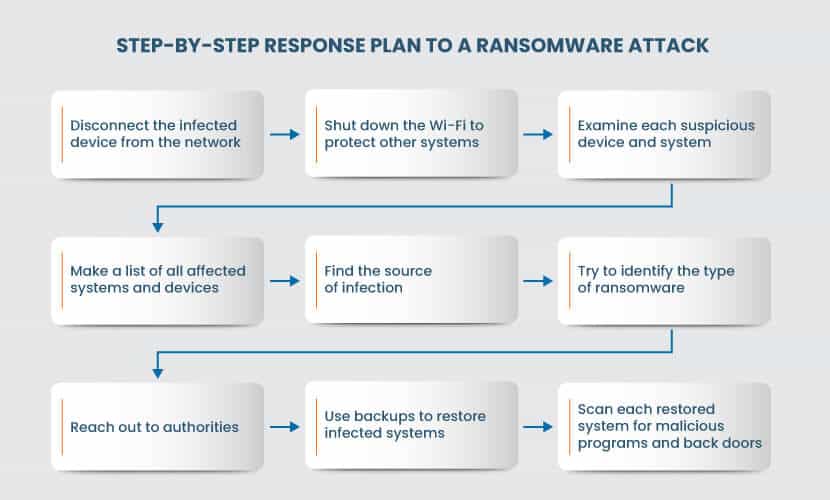
Even the best ransomware protection is sometimes not enough to prevent an attack. If you suffer an attack, follow the steps below to minimize the damage and quickly return to business as usual:
- Isolate the problem. Take the infected device offline and shut down the network. The program is likely looking for other devices and drives, so remove the possibility of lateral movement.
- Assess the damage. Examine each suspicious device. Check for encrypted data, files with strange extensions, and reports of users having trouble opening files. Make a list of all affected systems, including network devices, cloud storage, external hard drives, laptops, PCs, portable devices, etc.
- Locate patient zero. You must identify the source of the attack. Look for alerts from your anti-virus and malware programs, EDR system, and monitoring platform.
- Identify the ransomware. You need to determine the type of ransomware that attacked your company. Most ransom notes reveal the attacker, but you can also type the message text into a search engine and identify the attacker that way.
- Contact the authorities. Police can help identify the attacker, plus there is also a chance that officers have the decryption key for the ransomware in question.
- Use backups to restore data. Restore each infected system from a backup. If you have immutable backups, the attack could not affect the backup file, so restore each device to the last safe state. Next, use an anti-malware solution to scan devices for back doors.
If you do not have a viable backup and the police do not possess the decryption key, your options are to either pay the ransom or cut your losses. Paying the ransom may not be the best idea, however, as we explain below.
Read our step-by-step guide on how to recover from a ransomware attack.
Should Companies Pay the Ransom?
If a company does not have a data backup and faces weeks or months of recovery, paying the ransom is tempting. However, consider the following before making the decision:
- There is a chance you never get the decryption key. Many victims have paid the ransom only to receive nothing in return.
- The decryption key may not work. Ransomware creators are not in the file recovery business, so criminals do not spend much time ensuring the decryption works.
- Your files may be too corrupted. Some ransomware programs corrupt files beyond repair to ensure encryption happens as quickly as possible. If that is the case, even a decryption key will be unable to restore the files.
- You become a worthwhile target. A company with a history of paying the ransom is an attractive target for a new attack. The same team may strike again in the future or let their colleagues know about what companies are willing to meet the demands.
- Criminals can still leak your data. If attackers exfiltrate your data, nothing can stop them from selling the data to the highest bidder even if you pay the ransom.
Instead of weighing whether paying the ransom is the right move or not, ensure your company can handle a ransomware attack. With the proper precautions and backups, you will never be in a position where you must consider paying the ransom.

Do Not Take Any Risks with Extortion Software
The best way to counter ransomware is to set up sound prevention tactics backed by a well-oiled response plan. Use this article to educate your team about the threat and set up precautions that ensure you can reliably prevent and recover from a ransomware attack. Also, learn more about the differences between Malware vs Ransomware and how they work in our detailed guide.