Introduction
Fail2ban is a software that protects your server from brute force attacks. It does this by monitoring server logs and detecting any suspicious activity.
The program detects when there is an unreasonable number of failed attempts and automatically adds new to iptables that block the given IP. This IP (or host) is then blocked for a specified time or indefinitely.
Therefore, installing this log-monitoring software is an excellent way to provide another layer to your server security. Still, can only be one part of your overall server security plan. Explore more measures with these 21 Server Security Tips.
In this tutorial, you will learn how to install and configure Fail2ban on your server.
Prerequisites
- Access to a command-line / terminal window
- Access to a user account with sudo or root privileges
Install Fail2ban
How to install Fail2ban depends on the operating system running on your server. Below you will find commands for installing and enabling Fail2ban on Ubuntu, CentOS, Fedora, and Debian.
Important: Fail2ban is not a replacement for software firewalls, such as iptables. It is intended as another security layer and should not be a replacement for a firewall.
Install Fail2ban on Ubuntu
1. Before adding new packages, it’s important to update the system repository and upgrade software. To do so, run the command:
apt-get update && apt-get upgradePress y to confirm and hit Enter.
2. Now you can install Fail2ban with:
apt-get install fail2ban3. Optionally, you can install Sendmail for email support:
apt-get install sendmail4. Next, you need to allow SSH access through the firewall:
ufw allow ssh5. Finally, enable the firewall:
ufw enableInstall Fail2ban on CentOS
1. To install Fail2ban on CentOS, you need the EPEL repository. Update the system and add the repository by running:
yum update && yum install epel-release2. With the EPEL repository set up, install Fail2ban with the command:
yum install fail2ban3. Next, you need to start the Fail2ban service and enable it upon boot:
systemctl start fail2bansystemctl enable fail2ban4. For email support, you can install Sendmail with:
yum install sendmail5. To start and enable Sendmail service run:
systemctl start sendmailsystemctl enable sendmailInstall Fail2ban on Fedora
1. Start by updating the system:
dnf update2. Then, install Fail2ban and Sendmail (optional, if you need email support):
dnf install fail2bandnf install sendmail3. As these services do not start automatically on Fedora, you need to start and enable them with:
systemctl start fail2bansystemctl enable fail2bansystemctl start sendmailsystemctl enable sendmailInstall Fail2ban on Debian
1. Update and upgrade the system:
apt-get update && apt-get upgrade -yPress y and Enter to confirm.
2. Then, install Fail2ban with the command:
apt-get install fail2ban3. For email support, you can also install Sendmail using the command:
apt-get install sendmail-bin sendmailNote: Check out our comprehensive comparison of CentOS vs Ubuntu for web servers.
Configure Fail2ban
Configure Fail2ban by editing the following configuration files:
- fail2ban.local file
- jail.local file
Configure fail2ban.local File
Fail2ban defines its global configuration in the fail2ban.conf file. The file consists of the default configuration and is generally not advised to modify.
All changes to the configuration should be done in a separate fail2ban.local file.
1. Therefore, the first thing to do is to copy the content of the .conf file into a .local file. The command to do so is:
cp /etc/fail2ban/fail2ban.conf /etc/fail2ban/fail2ban.local2. There will be no output after this command. The next step is to open the fail2ban.local file using a text editor of your choice:
nano fail2ban.local3. You should see a file similar to the image below:
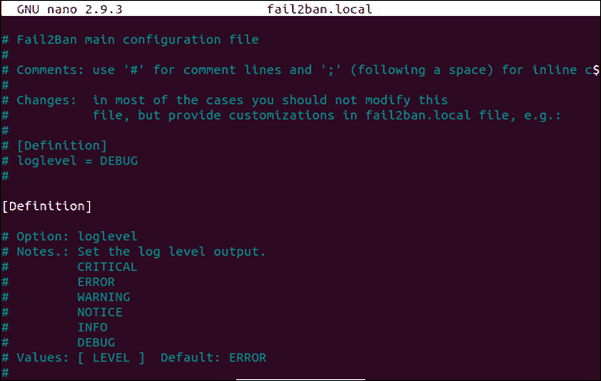
In this example, the comments in blue explain each option and its possible values. The white lines are the options you can modify and they include:
loglevel– Set the log level output toCRITICAL,ERROR,WARNING,NOTICE,INFO, orDEBUG.logtarget– Set the log target, which can be either aFILE,SYSLOG,STDERR, orSTDOUT.syslogsocket– Set the syslog socket file toautoorFILE(this is only used if thelogtargetis set toSYSLOG)socket– Set the socket file which is used to communicate with the daemon. Make sure not to remove this file. It’s default path is:/var/run/fail2ban/fail2ban.sockpidfile– Set the PID file which is used to store the process ID of the fail2ban server. The default location is:/var/run/fail2ban/fail2ban.pid
Configure jail.local File
Another Fail2ban configuration file you may need to modify is the jail.conf file which includes jails defining Filters with Actions.
Just like with the global configuration, the jail.config file should not be directly modified. Instead, all customization should be made in the jail.local file.
1. If you do need to make some changes, copy the content of the .conf file into a .local file:
cp /etc/fail2ban/jail.conf /etc/fail2ban/jail.local2. Open the jail.local file with a text editor of your choice:
nano jail.local3. You should see the following content:
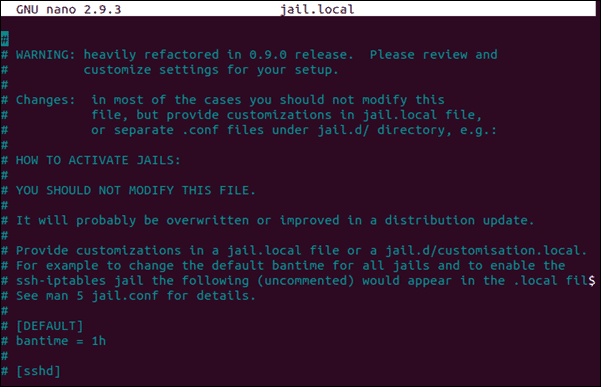
There you can set the following options:
ignoreself– Specify if the local IP address should be ignored by setting the valuetruefalse.ignoreip– Allows you to specify IP addresses, CIDR masks or DNS hosts which should be banned. Separate multiple addresses with space.ignorecommand– Define thepath/to/commandif one should be ignored.
bantime– Specify the number of seconds a host is banned (the default being600)maxretry– The number of failures allowed before a host is banned (by default set to5).findtime– The time in which the host should not use up themaxretrynumber in order not to get banned (generically set to10minutes). For example, if a host fails 5 times in 10 minutes, it gets banned for 600 seconds.
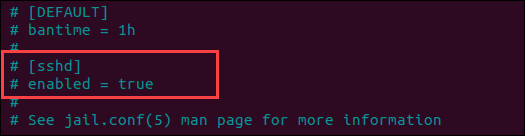
backend– Specify the backend used to get files modification. If you are using CentOS or Fedora, you need to set the backend tosystemd. The default valueautois sufficient for other operating systems.[ssh]– by default, Fail2ban has no enabled jails. Therefore, you need to do this manually by adding the jails to the configuration file. For instance, you can enable the SSH daemon jail by uncommenting (removing#) the lines[ssh]andenabled = true.
destemail– Specifies the email address where you want to receive notificationssender– Defines the email address from where you receive notifications
Additional jail.local Configurations
You can also set additional configurations in the jail.local file, such as for SSH and iptables. These options include:
banaction– Specifies the default action that is used when themaxretryis reached.banaction_allports– Allows you to label an IP that should be blocked in every port.port– The value should correspond to the set service. This could besshor a port number (if you are using an alternative port).filter– The file name containing the failregex information, located in/etc/fail2ban/filter.d.
Restart the Service
If you have made any changes to the fail2ban.local and jail.local files, make sure to restart the fail2ban service.
To restart the fail2ban service with the new configuration, run the command:
service fail2ban restartConclusion
By following this guide, you should have been able to install and set the basic configuration for Fail2ban.
Fail2ban is an excellent tool for adding another security layer. It is especially effective against SSH brute force attacks.